Business Email Compromise
Business Email Compromise (BEC) Scams are one of the most financially damaging online crimes. Also known as Email Account Compromise (EAC), it exploits email which we use to conduct business daily – both personally and professionally.
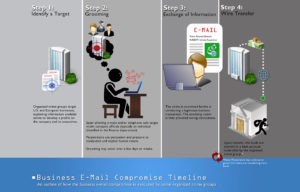
An example would be:
Protect yourself today from Business Email Compromise (BEC) Scams.
https://www.breachsecurenow.com/2018/10/02/business-email-compromise-scams-stay/
Where to go for more information or to get in contact with the CCP Team?
Please visit our website (www.ccpteam.com) or check us out on social media if you’re interested in learning more. As always, calling our office will result in hearing a friendly voice that is happy to discuss any questions you may have. We’ll keep pushing in the direction of excellence and look forward to those continuing partnerships that drive IT Success for Business